Scanning process
Create scan process
The scanning process is always recommended to be done from the slave and then imported into the corresponding master.
After configuring the credentials, the first scan is executed:
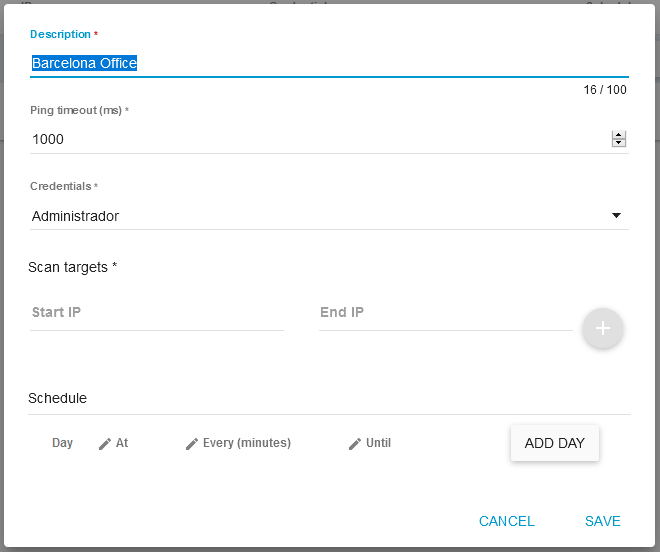
- Description: A representative description of the scanning process
- Ping Timeout (ms): Time that STND waits for the device being scanned to give a response
- Credentials: Select the credentials you want to scan with, they refer to the credentials registered in the previous section
- Scan targets: The range of the IPs to be scanned. Several ranges can be added by clicking on the "+" button
- Schedule: Specify when the process should be initiated, or if it will be recurrent over a period of time
Attachments

Help Desk Software
ServiceTonic